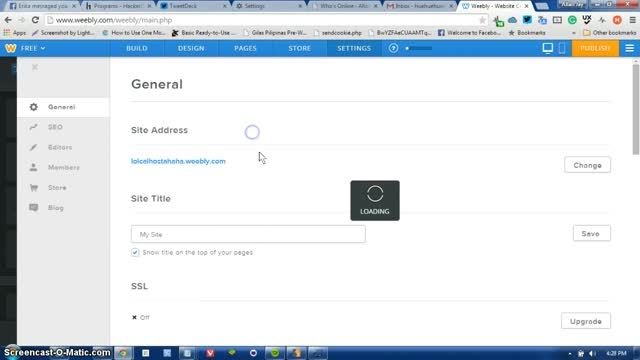
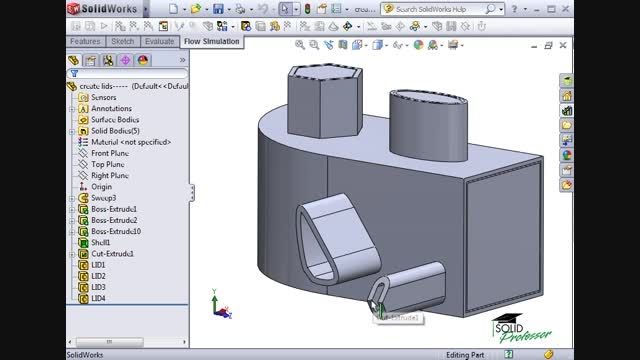
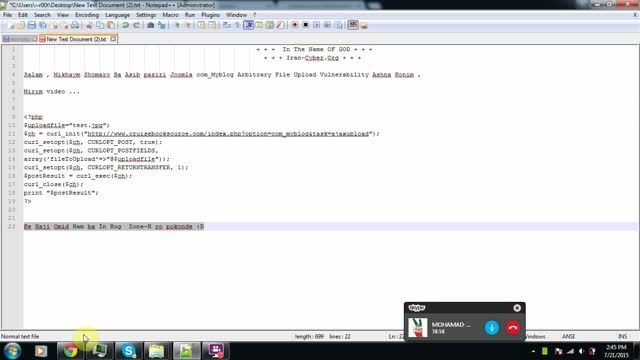
Finding DLL Hijacking vulnerability manually
301 بازدید
301 بازدید
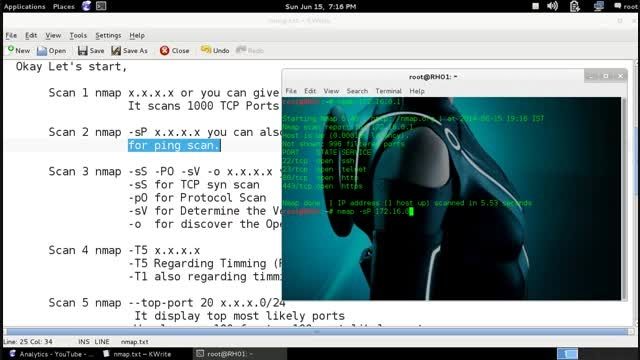
From Obfuscated password to Brute Force to Account Compromise; in this demo, we try to recover clear-text password characters that are encapsulated in challenge-response based application traffic. It should be noted that even though sensitive information is not revealed in plain-text, there will be ways to recover it unless the application implements public-key cryptography. If you'd like to repro
اولین نفری باشید که برای این ویدیو دیدگاه ارسال میکنید