جستجو برای:
Obfuscated
-
 1:49
1:49
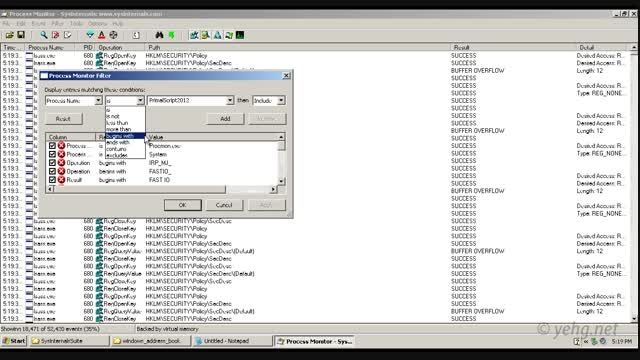
Finding DLL Hijacking vulnerability manually - in this demo, we attempt to hijack DLL files that was loaded by a software installer from the directory where the installer is executed.
-
 4:09
4:09
From Obfuscated password to Brute Force to Account Compromise; in this demo, we try to recover clear-text password characters that are encapsulated in challenge-response based application traffic. It should be noted that even though sensitive information is not ...


